So, at first I wanted to make sure the script worked and I used test.txt, ran it through my python script using 'python xor_obfuscator.py -i test.txt -p john' and left the output file as the default value. Then, to double check that it worked, I ran 'python xor_obfuscator.py -i out.file -p john -o new.test.txt' and verified that it worked with md5 sum.
As we can see, the 'test.txt' and 'new.test.txt' have the same md5sum but after obfuscating with password 'john' the md5sum changes. Now, let's try this with a meterpreter shell.
We're going to use msfvenom to create a simple meterpreter executable and we'll run it through VirusTotal to determine if it can still detect the executable.
Here we've created the meterpreter.exe and the hidden.exe.obf.
Interestingly enough, VirusTotal didn't do a great job detecting even the simple meterpreter payload but, some AVs did detect the meterpreter.exe file.
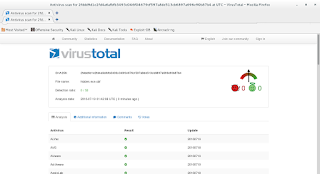
Now, after we scan the hidden.exe.obf file...
0% detection! This makes sense because the file virtually does not resemble an executable anymore nor could you execute it as such BUT, you could place this on a target and according to this it wouldn't be detected.
This is not a sophisticated method for hiding executables but it could work to avoid simple antivirus, firewall, and intrusion detection systems. Do with it what you will!
--EDIT-- 7/19/2016
I was able to add random password creation and execution via temporary files to my python script. Check out the updates at the same link as above but, here it is again: https://github.com/Quantumite/xor_obfuscator/





No comments:
Post a Comment